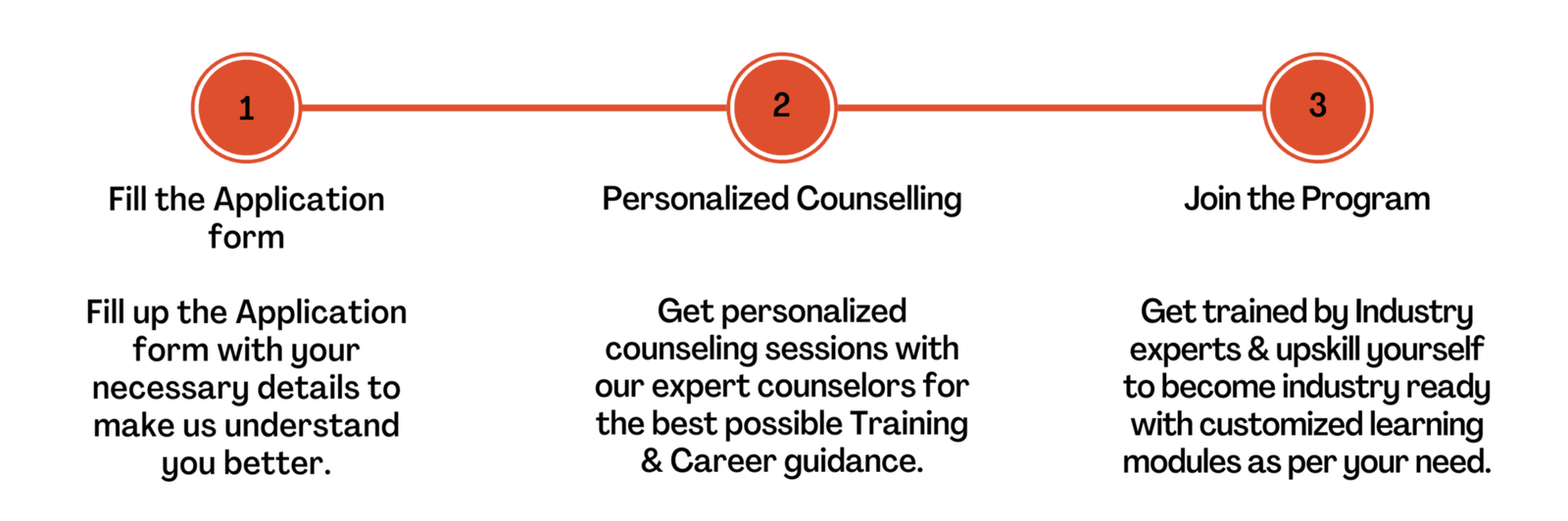
Join the community of learners, creators, professionals, educators, and world-changers.
Learn, certify,
make an impact.
Expand your career opportunities with the Python Institute’s training and certification programs. Program your future.